Mastering Safety and Security
with Industry-Leading
Certification
Get Started
About Us
Unical Academy specializes in providing comprehensive training and certification in safety and security. With a focus on industry standards and best practices, our programs are designed to equip professionals with the knowledge and skills needed to excel in fields that prioritize safety and security. Our courses ensure that participants are well-prepared to meet the rigorous demands of certification processes, contributing to their professional growth and the overall security of the systems they work with.

Happening in the world
What We Teach vs. Real-World Attacks: How CEH v13 Actually Aligns with Today’s Threats
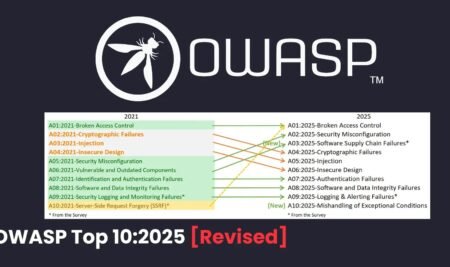
OWASP Top 10: 2025
Proposed Indian Military Airworthiness Bill 2024: Elevating Aircraft Safety
DO-178 software reuse in the ISO 26262 domain reduces cost for automotive suppliers
Popular Articles
From Certification to Job-Ready: How Unical Academy Trains Ethical Hackers for the Real World
The global demand for cybersecurity professionals has never been higher. With organizations across industries facing sophisticated cyber threats, certifications...
What We Teach vs. Real-World Attacks: How CEH v13 Actually Aligns with Today’s Threats
A common criticism of cyber security certifications is that they are “theoretical” or “exam-focused.” In reality, the value of...
CEH v13 Classes Starting Soon – Ethical Hacking Training with AI at Unical Academy
Hands-On | AI-Driven Ethical Hacking Cyber security threats are evolving faster than ever, and organizations today require professionals who...
White Papers
DO-178C: Complete Software Life Cycle
Understanding DO-178C Certification Artifacts
Requirements-Based Testing for DO-178C
Popular Articles
From Certification to Job-Ready: How Unical Academy Trains Ethical Hackers for the Real World
The global demand for cybersecurity professionals has never been higher. With organizations across industries facing sophisticated cyber threats, certifications...
What We Teach vs. Real-World Attacks: How CEH v13 Actually Aligns with Today’s Threats
A common criticism of cyber security certifications is that they are “theoretical” or “exam-focused.” In reality, the value of...
CEH v13 Classes Starting Soon – Ethical Hacking Training with AI at Unical Academy
Hands-On | AI-Driven Ethical Hacking Cyber security threats are evolving faster than ever, and organizations today require professionals who...
Latest News
News all over the world.
From Certification to Job-Ready: How Unical Academy Trains Ethical Hackers for the Real World
Beware of Weaponized Notezilla, RecentX, & Copywhiz Windows Tools that Deliver Stealing Malware
WordPress Releases Urgent Security Update to Patch XSS and Path Traversal Flaws
HC3 Unveils Qilin Ransomware Attacking Global Healthcare Organizations
Popular Course
Limitless learning, more possibilities
GET 100 OF ONLINE COURSES FOR FREE
REGISTER NOW
Create your free account now and immediately get access to 100s of online courses.
[contact-form-7 id=”13917″ title=”Contact Home Page”]
Why Choose Us?
A choice that makes the difference.
Interactive Learning Platform
Career Development Resources
Certification
Events
From Concept to Celebration.

Difference between DO 178B & DO 178C
DO-178B and DO-178C are crucial standards for developing airborne software systems. While DO-178C builds on the foundation of DO-178B, it introduces several significant enhancements...

RTCA’s Standards Evolving with new Airspace Operations – DO-178()
RTCA’s Software Standards are the backbone of deterministic software operation in aviation. Panelists include FAA, an AAM Operator and others.
What People Say
How real people said about us
Akshitha
“ LearnPress is a comprehensive LMS solution for WordPress. This WordPress LMS Plugin can be used to easily create & sell courses online. Each course curriculum can be made with lessons & quizzes which can be managed with easy-to-use user interface, it never gets easier with LearnPress. ”
Bhadri
“ LearnPress is a WordPress complete solution for creating a Learning Management System (LMS). It can help me to create courses, lessons and quizzes and manage them as easy as I want. I've learned a lot, and I highly recommend it. Thank you. ”
Ganesh
“ You don't need a whole ecommerce system to sell your online courses. Paypal, Stripe payment methods integration can help you sell your courses out of the box. In the case you wanna use WooCommerce, this awesome WordPress LMS Plugin will serve you well too. ”
Lasya
“ Education WP Theme is a comprehensive LMS solution for WordPress Theme. This beautiful theme based on LearnPress - the best WordPress LMS plugin. Education WP theme will bring you the best LMS experience ever with super friendly UX and complete eLearning features. ”
Manju
“ Education WP is a special build for an effective education & Learning Management System site. Education WP is the next generation & one of the best education WordPress themes which contains all the strength of eLearning WP and comes with better UI/UX. ”
Navya
Subscribe now and receive weekly newsletter with educational materials, new courses, interesting posts, popular books and much more!