Microsoft has unveiled a suite of new tools within its Azure AI Studio. These innovations are designed to address the growing concerns around prompt injection attacks, content reliability, and overall system safety, marking a pivotal step in the evolution of …
The critical vulnerabilities in JumpServer’s Ansible that allowed attackers to execute arbitrary remote code have been patched. With a CVSS base score of 10, the critical vulnerabilities identified as CVE-2024-29201 and CVE-2024-29202 impact versions v3.0.0-v3.10.6. A jump server is an intermediary device that …
An automated risk detection system identified a typosquatting campaign targeting popular Python libraries on PyPI. In two waves with a 20-hour break, the attack deployed over 500 variations with typos in names like requests, TensorFlow, and BeautifulSoup. The campaign included …
Guardio Labs has uncovered a significant vulnerability in Microsoft Edge, Microsoft’s flagship web browser, that could allow hackers to install malicious extensions without the user’s knowledge. This flaw, if exploited, could lead to a range of security breaches, including data theft, privacy …
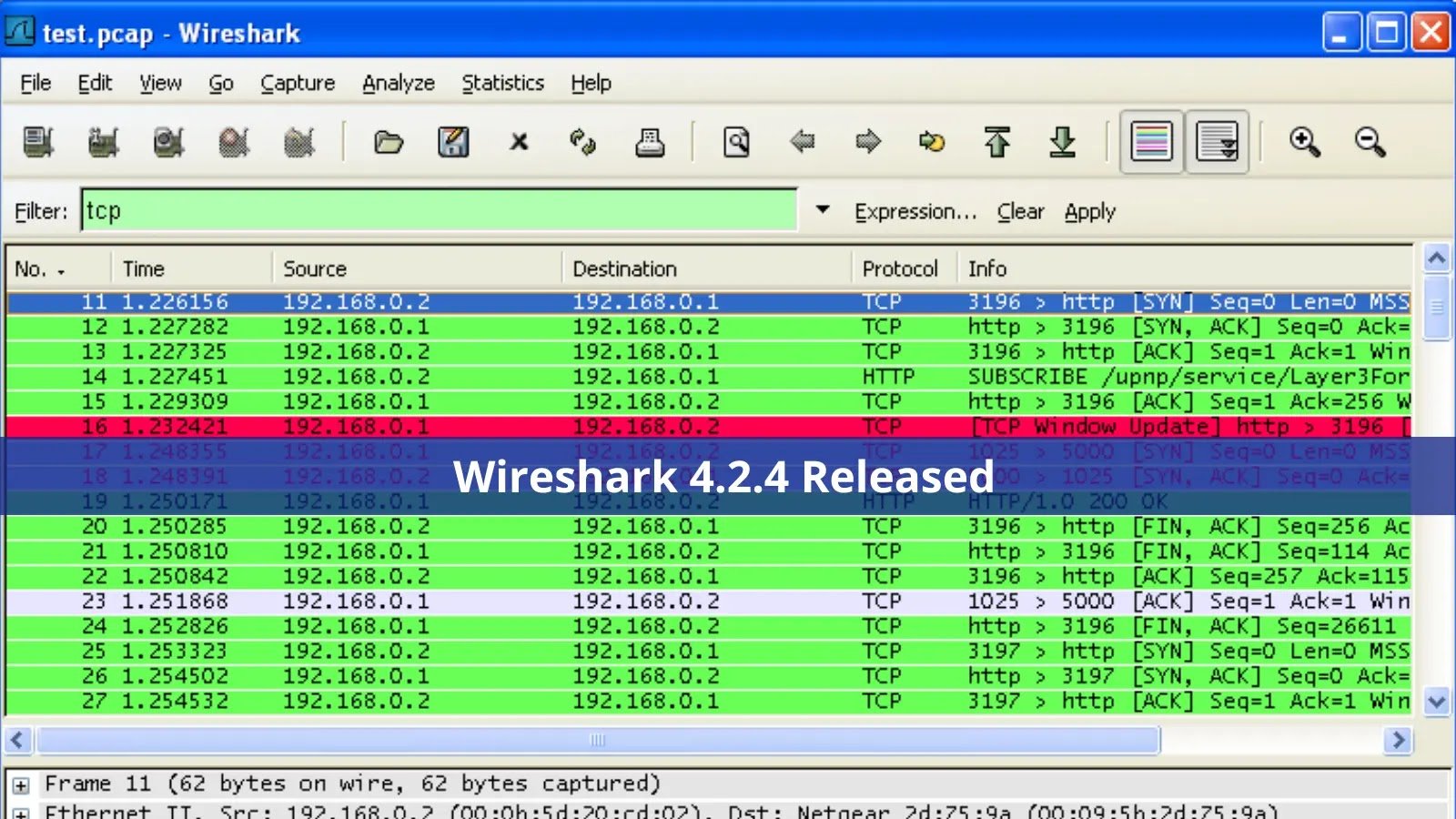
Wireshark remains the go-to choice for both professionals and enthusiasts due to its unmatched capabilities in packet capturing and analysis. Its advanced features and user-friendly interface make it an indispensable tool for network troubleshooting and protocol analysis. The latest release, …
Splunk Inc. has disclosed two significant vulnerabilities within its software suite, posing a considerable risk to organizations utilizing Splunk Enterprise and Splunk Cloud Platform. The vulnerabilities, identified as CVE-2024-29945 and CVE-2024-29946, have been rated high in severity with CVSS scores …
A significant vulnerability has been identified in the Rank Math SEO plugin for WordPress. This flaw, cataloged under CVE-2023-32600, exposes over two million websites to potential cyber-attacks, posing a severe security risk to online businesses and content creators reliant on this …
Unsaflok, in Dormakaba’s Saflok electronic RFID locks used in hotels and multi-family housing, allows attackers to forge a master keycard by exploiting weaknesses in the system and then using it to unlock any door within the affected property. The vulnerability …
The Mobile Security Framework (MobSF), a widely used pen-testing, malware analysis, and security assessment framework, has been found to contain a critical input validation flaw that could lead to server-side request forgery (SSRF) attacks. The vulnerability, tracked as CVE-2024-29190, affects MobSF …
As tax season rolls around, a period marked by the rush to meet filing deadlines and ensure compliance with tax laws, cybercriminals are ramping up their efforts to exploit this busy time. Leveraging sophisticated social engineering tactics, these threat actors launch targeted …