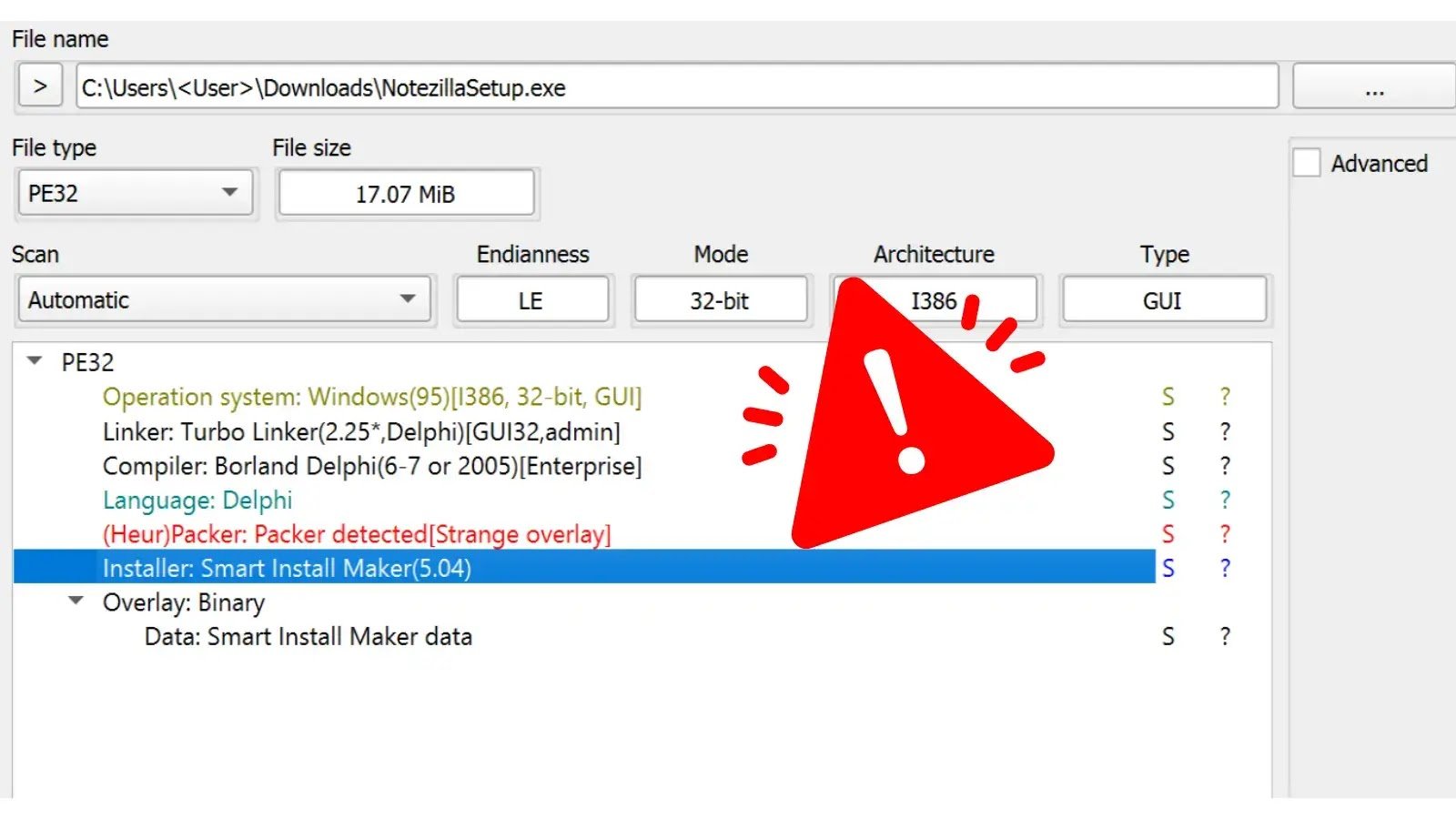
Cybersecurity firm Rapid7 has identified that popular Windows tools Notezilla, RecentX, and Copywhiz have been weaponized to deliver malware. These tools, developed by Conceptworld, an India-based company, are widely used for productivity enhancements. However, the installation packages available on the …
WordPress has released an urgent security update, version 6.5.5, addressing critical vulnerabilities that could potentially compromise the security of millions of websites. This minor release, which also includes three bug fixes in the core, is highly recommended for immediate installation to ensure …
The Health Sector Cybersecurity Coordination Center (HC3) has issued a critical alert regarding a new ransomware strain, Qilin, which is targeting healthcare organizations worldwide. This revelation underscores the escalating cyber threats facing the healthcare sector, which is already grappling with the complexities …
The Cybersecurity and Infrastructure Security Agency’s (CISA) Chemical Security Assessment Tool (CSAT) was the target of a cybersecurity intrusion by a malicious actor from January 23-26-2024. The breach, which has raised significant concerns within the cybersecurity community, potentially exposed sensitive information including …
ESET, a leading cybersecurity company, recently addressed a local privilege escalation vulnerability in its Windows security products. The Zero Day Initiative (ZDI) reported the vulnerability to ESET. It could have allowed attackers to misuse ESET’s file operations during a restore operation from …
Researchers analyzed real-world passwords leaked on the dark web instead of artificial ones used in labs, as their findings showed that a worrying 59% of these passwords could be cracked within an hour using just a modern graphics card and …
A newly discovered security vulnerability allows attackers to impersonate Microsoft corporate email accounts, significantly increasing the risk of phishing attacks. Security researcher Vsevolod Kokorin, also known as Slonser, found this bug, which Microsoft has not yet patched. Kokorin revealed the …
Hackers often abuse weaponized Word docs, as they can contain macros that contain or exploit flaws inside those Word files to run destructive code upon being opened by the intended victims. It enables an attacker to employ this tool to …
Microsoft has announced a new way to spot potentially hacked machines in your organization. Analysts may now easily identify, examine, and search for suspicious interactive processes running on “hidden desktops” using Defender for Endpoint’s “DesktopName” field. These days, remote desktop protocol …
Cybersecurity researcher Jeremiah Fowler discovered a non-password-protected database containing 474,651 images belonging to Total Fitness, a health club chain with 15 locations across North England and Wales. The database, which was 47.7 GB in size, included personal screenshots, profile pictures of members …